Control and record remote access to servers and network devices
Many organisations need external and internal users to access servers and network devices. That access is often ad hoc, hard to audit and increases exposure when credentials are shared or unmanaged.
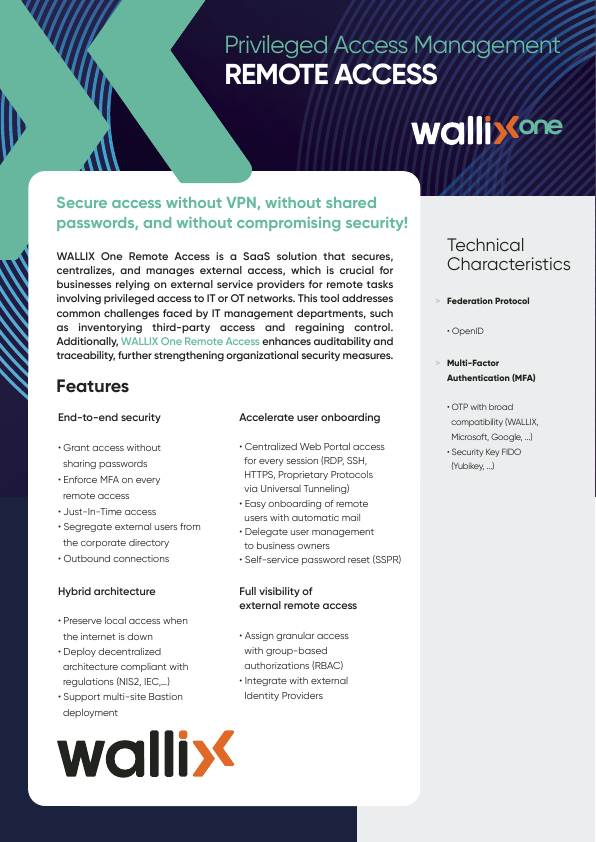
WALLIX Remote Access enables controlled, logged and recorded remote connections. It enforces authentication and authorisation, centralises access control and stores session records and audit data so teams can review activity and maintain accountability.
Where WALLIX Remote Access is used
Grant and monitor vendor or third‑party access to on‑prem servers and network kit while keeping a central audit trail. Use recorded sessions to review actions taken during maintenance or troubleshooting.
Provide auditable privileged sessions for internal administrators, capture session logs for investigations, and centralise access data to support operational governance across mixed estates.
Fits within these solutions
Delivery & Deployment
Suitable environments
Fits mid‑market and larger organisations, public sector bodies and regulated firms that need traceable remote access. It suits businesses with distributed or hybrid estates and teams that manage privileged access without outsourcing operations.
Benefits
Improved accountability
Clear records of who accessed which systems and what actions they performed.
Enhanced auditability
Centralised logs and session recordings make technical reviews and audits feasible.
Reduced credential exposure
Avoid shared or persistent credentials by mediating access through controlled sessions.
Faster investigation support
Session recordings and logs speed up root‑cause analysis after incidents.
Consistent visibility
Single view of remote activity across mixed estates and user types.
Third‑party control
Apply the same controls and audit trail to external vendors as internal staff.
Capabilities
Authentication enforcement
Authorisation controls
Access logging
Session recording
Centralised access control
Servers and network support
Audit data centralisation
Applications
Third‑party vendor access
Grant and audit remote access for external service providers without sharing local credentials.
Privileged administration
Provide time‑bound, monitored sessions for administrators performing high‑privilege tasks.
Remote troubleshooting
Allow vendors or internal teams to perform diagnostics while recording activity for review.
Evidence for audits
Use central logs and recordings as technical evidence during audits and reviews.
Hybrid estate control
Manage remote access consistently across on‑premises and distributed infrastructure.
Incident analysis
Replay recorded sessions and consult logs to reconstruct actions during security investigations.