Heimdal Application Control — allowlisting and execution control for endpoints
Malicious and unauthorised applications still reach endpoints and increase incident risk. Organisations need deterministic control over what runs on company devices to reduce exposure and simplify investigations.
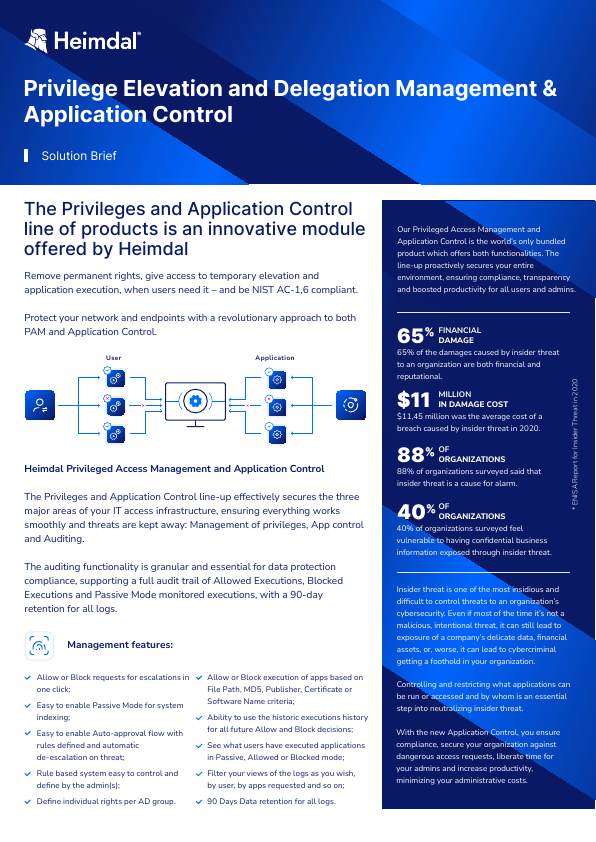
Heimdal Application Control lets administrators centralise allowlists and execution rules so only approved binaries run. It blocks unauthorised execution and lowers the chance of unwanted software running on managed devices.
The product is relevant where teams require clear, enforceable control of endpoint behaviour—for example in regulated sectors, remote or hybrid workforces, or where security staff are small.
Where Heimdal Application Control is used
Lock down corporate laptops and shared workstations to prevent installers and unauthorised tools from executing. This reduces the number of usable attack vectors and narrows what responders must investigate.
Harden admin and sensitive user stations by restricting which utilities and scripts can run, lowering the risk of privilege misuse or lateral movement.
Suitable for MSPs and IT teams that need repeatable, centrally managed policies across customer or business units, especially where endpoints are predominantly Windows.
Suitable environments
Best fit where Windows endpoints predominate, teams need central policy control, and security staff are small or stretched. It helps organisations with remote or hybrid work patterns enforce consistent execution rules.
May be less suitable where estates are highly heterogeneous with large numbers of non-Windows devices or where organisations expect a managed detection or 24x7 monitoring service. The product focuses on execution control rather than outsourced monitoring.
Benefits
Reduce attack surface
Limits which applications can run on endpoints, reducing exposure to malware and unauthorised software.
Prevent unauthorised software execution
Stops unapproved applications from running, reducing the risk of compromise.
Improve endpoint security
Strengthens endpoint protection by enforcing strict control over software execution.
Support Zero Trust security models
Applies a default-deny approach to application execution, allowing only trusted software to run.
Reduce security incidents
Prevents malicious or unwanted software from executing, lowering the likelihood of endpoint compromise.
Increase visibility of application usage
Provides insight into which applications are running and being blocked across the organisation.
Enforce consistent policies
Applies standardised application control policies across all managed endpoints.
Capabilities
Application allowlisting
Application blocking
Policy-based execution control
Privilege-aware application control
Trusted sources and publishers
Real-time execution enforcement
Centralised policy management
Reporting and audit
Applications
Control which software can run
Used to ensure only approved applications can execute across endpoints.
Reduce ransomware and malware risk
Prevents unauthorised executables from running, blocking common attack vectors.
Support Zero Trust endpoint security
Applies a default-deny approach to application execution in line with Zero Trust models.
Lock down high-risk endpoints
Restricts software execution on sensitive or exposed devices such as kiosks or shared systems.
Control shadow IT applications
Prevents users from installing or running unauthorised applications.
Enforce application compliance policies
Ensures only approved and compliant software is used across the organisation.
Reduce reliance on detection-based security
Prevents threats before execution rather than relying solely on detection and response tools.
How we help
Armstrong may support implementation, configuration and ongoing support for Heimdal Application Control. Engagements typically involve SMEs and mid-market businesses, MSP customers, organisations with mainly Windows endpoints, remote or hybrid workforces, regulated sectors, and organisations with small or no dedicated security teams.