Title
Finding a balance between having control over sensitive operations in Active Directory and not spending too much valuable time on them is very hard. High level authorities can’t afford to perform all simple and time-consuming operations themselves. But at the same time they need to retain full control over them.
Is there a way out of this problem? Yes. With Adaxes there is a solution. It allows to add an approval step to practically any operation performed in Active Directory, Exchange, Office 365, etc. This means that the actual execution of various tasks can be delegated to lower level authorities without sacrificing the control.
How It Works
Let’s have a look at how approval-based workflow can be useful in a real world.
Take a company that has a typical structure. Obviously, it does have an IT department, where Tim is working as an admin.

User Creation Process
Among other duties Tim is responsible for user accounts creation, maintenance and deprovisioning. Fortunately, his managers are wise enough to understand that making a highly skilled admin to perform such routine tasks is equivalent throwing his salary away. That is why they make a right decision and get Adaxes.
With Adaxes Tim can delegate all user creation procedures to the HR department. Previously there was a risk that there would be a mistake and, for example, some users would be created in a wrong OU or several accounts for the same user would be created by accident, etc. But now Tim can be calm about that.

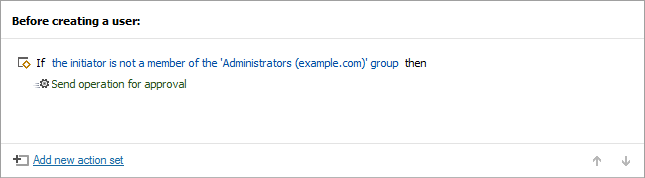
All he needs to do is to create an approval step that would be triggered before user creation. Once somebody from the HR department enters all the personal data of a new employee and clicks the Create button, the operation will be suspended and an email notification with an approval request will be sent to Tim.
After checking that everything is alright, Tim will grant his permission. Only then the user account will be created. If there is something wrong with the new user, Tim can deny the operation. This approach allows him to spend significantly less time on the tedious user creation process but still retain full control over it.
Group Membership Management
Another area where Tim’s managers would like him to spend less of his extremely valuable time is managing users’ group membership for things like printer access, shared folders, etc.
Previously, if users required access to any of the company resources, they needed to email the IT department to request it. Admins then had to check if this user really needs these access rights, sometimes ask their managers, etc.
It’s easy to spot that this was really far from being efficient.
But with Adaxes admins can be excluded from this chain and at the same time still have full control over the process. Users can be enabled to add themselves to groups but only after an approval is granted. For example, it can be requested either from the users’ managers or from group owners.
The great thing is that there are no specific technical skills required from the managers, so no extra training or whatsoever is needed. All they need to do is get an email, check if a particular user really needs new access rights, proceed to the Web UI and either approve or deny the operation. As simple as that!
Managers don’t even need to know that groups (or even Active Directory itself) exists. For them it will be a simple question of either allowing access to some resources or not. No further complications.

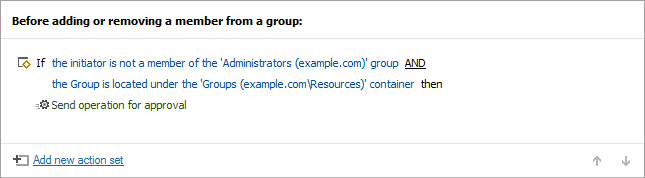
To enable all that, Tim creates a rule in Adaxes that would be triggered before a user is added to a group. The operation will then be suspended until an approval is granted.
Adaxes allows Tim to be very flexible when defining the approvers list. He can either choose a specific manager for each case or go for one of the predefined options: manager of the requestor, owner of the requestor’s OU, owner of the target group or owner of the target group’s OU. In that case the approvers list will be formed depending on the actual operation.
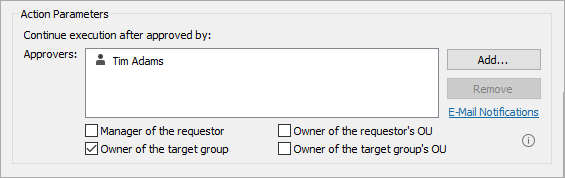
If Tim wants to create a more complicated list of approvers that will include, e.g. assistants of managers, or a list that would change depending on certain conditions, he can use his own custom scripts to extend the out-of-the-box functionality of Adaxes.
For some security sensitive operations he can add multi-level approval. This means that after the first permission is granted, e.g. by a manager of the requestor, Tim can add another approval step, putting, e.g. a higher level manager or members of IT staff in the approvers list. Thus the operation won’t proceed unless approved at all levels.
Of course, there might be a situation when a certain approver becomes unavailable, so the operation that are waiting for his permission get stopped. Naturally, nobody wants delays like that, so such situations have to be solved somehow. Luckily, Adaxes has got Tim covered in that case. Being an admin, he can always access all approval requests in the environment from the Adaxes Administration Console and approve/deny/cancel any of them if it is needed.
Controlling Automated Tasks
Approval mechanism of Adaxes allows Tim to delegate more operations to users whilst retaining full control over them. But what about tasks that have nothing to do with users? What about automated operations performed either regularly or triggered by certain events?
For example, Tim has got an AD cleanup process that runs periodically and deprovisions stale user accounts, deletes inactive computers, empty groups, etc. To make sure that nothing goes wrong, he can add an approval step to any of the operations that are performed automatically (e.g. automatically deprovisioning inactive users). Again, this would mean that the only thing he needs to do, is to check requests that are sent to him by email and approve/deny. This takes significantly less time than doing all the same by hand.
Conclusion
Implementing Approval-Based Workflow can significantly increase overall efficiency as it allows to delegate more responsibilities to lower level authorities without any compromises in security. Such approach can reduce the load on more skilled and high valued employees but at the same time keep them in charge of everything.
This leads to a generally healthier environment and gives businesses an opportunity to better allocate their resources and focus on the things that really matter.
Other Features
Active Directory Management
Adaxes features a rule-based platform for Active Directory, Exchange and Office 365 automation, provides an enhanced web-based management environment, gives you a role-based access control model for delegating privileges, adds security with approval-based workflow, allows enforcing corporate data standards and much more.
More InfoActive Directory Automation
Adaxes provides rule-based automation for Active Directory, Exchange and Office 365. It allows executing sets of operations that are governed by if/else conditions before or after certain events in AD. So, for example, after the department of a user is changed, Adaxes can then automatically update the user’s group membership and send an email notification to the user’s manager, following the rules you define.
More InfoActive Directory Provisioning
Using condition-based rules you can automate the entire user provisioning process. Once a new user account is created in Active Directory, Adaxes will automatically execute the rest of onboarding procedures for you: moving the user account to a correct OU, adding it to necessary groups, creating and configuring an Exchange mailbox, assigning Office 365 licences, enabling the user for Skype for Business, creating and sharing a home folder, sending a welcome email, etc. Similarly to that, you can also automate all operations associated with user updates. Finally, when a user is terminated, Adaxes can automatically execute all the provisioning operations in reverse, ensuring instant and errorless offboarding.
More InfoWeb Interface for Active Directory
Adaxes Web Interface enables Active Directory management via a standard web browser. It features a modern responsive design, so users can access it on their laptops, tablets, phones or any other devices. You can set up different Web Interfaces specifically tuned for the needs of different job roles, like administrators, help desk, HR, managers, and others, giving them a clean and intuitive way to access the tasks they need. Adaxes Web Interface also incorporates Exchange and Office 365 management, so users get a single console without the need to learn and use multiple tools for their day-to-day routines.
More InfoWeb Interface Customisation
The Adaxes Web Interface is fully customisable, so you can configure it to have the exact views, forms, and operations that each user needs. For example, administrators can have a full set of management activities in Active Directory, Exchange and Office 365 across the entire environment, whereas managers can be set to view just their subordinates and only be able to update their group membership, assign Office 365 licences and change certain AD properties.
More InfoActive Directory Self Service
Adaxes Web Interface can act as a self-service portal for regular users. You can granularly specify, which operations they have access to, like updating their personal info, changing their own password, searching Active Directory, managing own group membership, updating Office 365 licences, etc.
More InfoActive Directory Password Self-Service
Adaxes Password Self-Service allows users to reset forgotten passwords and unlock accounts by themselves. To do that they need to go through a simple identity verification procedure that may involve answering security questions, SMS verification, using authenticator apps like Google Authenticator, Authy and others. A self-password reset can be accessed from the Windows logon screen, Adaxes Web Interface or it can be integrated into your own portal.
More InfoExchange Management and Automation
Adaxes automates Exchange mailbox management both on-premises and in Office 365. For example, after creating a new user account in Active Directory, Adaxes can automatically create an Exchange mailbox for the user. The database distribution of mailboxes can be done based on the first letter of the users’ surname, least number of mailboxes in the DB, the round-robin method, etc. Adaxes can then configure the mailbox, e.g. modify storage quotas or enable mailbox features like Unified Messaging or Archiving.
More InfoOffice 365 Automation and management
Adaxes can automatically assign and revoke Office 365 licences using condition-based rules. For example, when a new user is created in Active Directory, Adaxes can activate an account in Office 365 for the user and assign the necessary O365 licences according to the rules you define. Different licences can be assigned to different users based on their job title, department, location, etc.
More InfoActive Directory Role-Based Security
Adaxes introduces Role-Based Access Control for Active Directory, Exchange and Office 365. In a role-based delegation model, instead of assigning permissions to users, they are assigned to roles that correspond to actual job functions. So, when you need to change privileges for all users with the same job function, all you need to do is modify the permissions of the associated role. Assigning roles to users is done in a centralised manner, allowing you to easily control, who can do what and where. With role-based delegation, you can granularly specify, which parts of Active Directory are visible to users. For example, you can allow certain users to only view AD objects located in their own OU, while hiding the rest of the Active Directory structure from them.
More InfoApproval-Based Workflow
Adaxes allows you to add an approval step to practically any operation in Active Directory, Exchange and Office 365. For example, you can delegate user creation to HR, but after they fill in the form and click Create, Adaxes can suspend the operation and only proceed once a member of IT staff reviews and approves it. For more complex and security-sensitive scenarios, you can set up multi-level approvals. Such an approach allows delegating more tasks to lower level staff without taking the risk of losing control over them.
More InfoActive Directory Reports
Adaxes comes with reporting capabilities, allowing you to monitor and analyse what’s going on in your environment. Out of the box, you get more than 200 reports, which should cover the majority of your requirements. For more demanding scenarios Adaxes also provides various ways to create custom reports, including using your own scripts. It enables you to create reports of practically any complexity that can be specific to your organisation's needs. To deliver reports to users Adaxes supports centralised scheduling and also provides a self-scheduling option, allowing users to choose by themselves, which reports they want to receive and when.
More InfoCustom Commands for Active Directory
With Custom Commands users can launch complex multi-step operations in one go. For example, if you need to send a user on vacation, you can do it with just one click in the Web Interface. The operation can include steps like disabling the user account, adding it to a corresponding group, sending a notification to the user’s manager, etc. Such an approach allows you to delegate complicated tasks to users and not worry that they will miss a step or do something wrong. Besides, you don’t over-privilege them, as you only give out permissions to execute the Custom Command as a whole, not the individual steps it consists of. Administrators can also use Custom Commands in their day-to-day routines to make the management process simpler and accomplish the same results with a lot fewer clicks.
More InfoScheduled Tasks for Active Directory Management
Adaxes allows you to automate various routine management tasks by scheduling them. For example, it can automatically de-provision inactive accounts in AD, allocate users to necessary groups, maintain OU structure, etc. You can also schedule tasks like importing new users from CSV. Automating such a sensitive operation doesn’t mean that you need to sacrifice any control, as you can add an approval step to it. This way users will be created in AD only after a member of IT staff reviews and approves the operation. You can also use scheduled tasks to send various notifications to users, like reminders about their password or account expiration.
More InfoActive Directory Delegation
Active Directory management involves many different operations that require administrative privileges granted by default to AD administrators only. Though operations like password reset or account unlock are pretty simple, they take a lot of time of highly-skilled IT staff, not allowing them to focus on more complex and important issues. Active Directory delegation helps you optimise the productivity of the IT department by letting non-administrative users (e.g. department managers or Help Desk operators) perform certain administrative activities in Active Directory.
More Info

